DevOps successfully unifies two traditionally separate aspects of the IT world: software development (Dev) and IT operations (Ops). By combining the people, processes, and technology of these entities, DevOps accomplishes its goal of shortening the systems development life cycle. The DevOps approach utilizes the Agile methodology to integrate and streamline the development and operations processes. This enables a faster and more efficient development process that provides continuous delivery of value and high-quality software.
As the spotlight focuses on speed, automation, and other DevOps tenets, security often becomes an afterthought and its negligence is a common shortcoming. Effective DevOps ensures rapid and frequent development cycles, but outdated traditional security practices can’t seem to keep up. Although the fast pace that DevOps promotes is part of what makes it so desirable, this velocity is simultaneously a downside as it can lead to additional security risks.
The solution is to integrate security protocols and practices across the entire DevOps pipeline and life cycle. DevOps security, or DevSecOps, is the application of information security (InfoSec) policy and technology to the entire DevOps lifecycle and value stream.
What security challenges have emerged from our DevOps initiatives? What practices have we implemented to overcome security gaps or challenges without hindering the benefits of DevOps practices?
Challenges in DevOps Security
The shift from monolithic applications to agile DevOps environments presents new risks and changes that traditional security solutions and practices cannot address. What new security challenges have emerged as a result of the modern, agile focus of DevOps?
- The fast-moving development process and environment can lead to security concerns caused by undetected bugs or errors. If security cannot move at the same speed as DevOps, it can lead to unintentional vulnerabilities, insecure code, and other weaknesses that contribute to operational dysfunction.
- The DevOps model is based on collaboration between different teams but these teams may have different processes, which can lead to gaps in security protocols. The highly interconnected and cohesive nature of collaboration in DevOps teams may also require unrestricted access to privileged accounts or the sharing of access keys, API tokens, certificates, etc. In turn, this opens dangerous backdoors and provides opportunities for malicious actors to attack, steal data, and disrupt operations.
- A large majority of DevOps environments rely on the extended usage of cloud (serverless) computing. To ensure complete support, the cloud provider needs to fulfill security requirements in compliance with an organization’s security processes and policies.
- Integrating security into CI/CD pipelines by including automated security testing to address vulnerabilities early and eliminate inefficiencies.
Best Practices for DevOps Security
The DevOps ethos has brought on a transformation and changed the way security needs to be achieved. Since DevOps involves every stage of the software development life cycle, effective security is more critical than ever. What principles and guidelines have we integrated to help deal with security challenges in a DevOps environment?
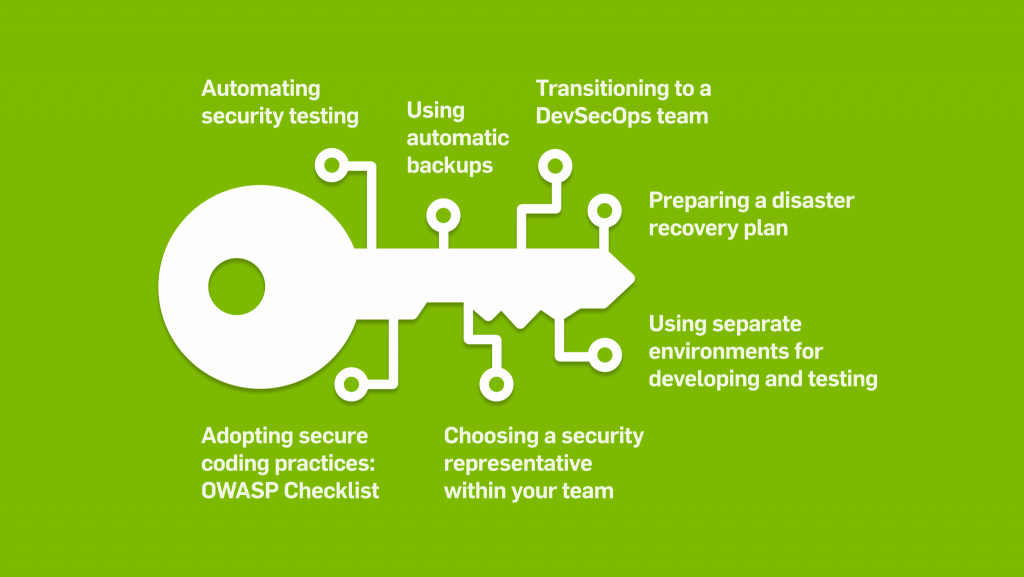
- Transition to a DevSecOps team. DevSecOps is an approach that brings together software development (Dev), security (Sec), and IT operations (Ops) to integrate security into the entire DevOps pipeline and life cycle. It’s essential for the DevOps team to take ownership of addressing security (rather than relying on an external provider) and for security to be included as early as possible in the development life cycle.
- The development team must adopt secure coding practices. For example, the OWASP Secure Coding Checklist is a comprehensive reference.
- Use tools for static code analysis and to highlight security flaws.
- Designate a member of the team to be responsible for security. Also make sure to use documented security procedures and policies that are easy for developers and other team members to comprehend.
- Use separate environments for developing, testing, and accessing production environments whenever possible.
- Make security a main concern in all testing phases and strategies.
- Follow a structured security testing methodology.
- Automate security testing as much as possible to scale security to DevOps processes. Security automation also minimizes the risk of human error and manual intervention.
- Use best practices in regards to credentials management to securely store and manage them.
- Run periodic manual and automated penetration testing on the production environments.
- Use containers whenever possible. Containers enable DevSecOps as they provide security and make rapid, repeatable application development and deployment cycles.
- Hack yourself. Assess your infrastructure and code from an attacker’s viewpoint to enable a better understanding of the security weaknesses and strengths of an application, service, data center, and cloud platform.
- Use automatic backups for critical information resources.
- Prepare a disaster recovery plan and test it periodically.
Despite the many benefits of DevOps, it presents new risks and security challenges that traditional solutions are unable to address. Although DevOps fuses development and operations processes, DevOps and security often still remain largely separate. To overcome this, DevOps security or DevSecOps aims to integrate security into all phases of the software development life cycle. From planning, developing, and testing to release, deployment, maintenance, and beyond.
Introducing DevOps security early in the life cycle enables a productive DevOps ecosystem. It helps to identify vulnerabilities and operational weaknesses long before they become an issue. By implementing the above DevOps security best practices, organizations will be empowered with the ability to reduce data breaches and to continuously deliver high-quality software at velocity, securely.
